Learn Computer Crime And Security Survey 2008 - Updated
Get computer crime and security survey 2008. 212008 CSI Computer Crime Security Survey The latest results from the longest-running project of its kind By Robert Richardson CSI Director For the 13 th year CSI has asked its community how they were affected by network and computer crime in the prior year and what steps theyve taken to secure their organizations. This survey of virtual communities and the threats they create to. Being fraudulently misrepresented as a sender of email messages requesting personal information B. Read also security and computer crime and security survey 2008 Employees abuse of Internet access or email.
Littlejohn Shinder Michael Cross in Scene of the Cybercrime Second Edition 2008. This process converts the original representation of the information known as plaintext into an alternative form known as ciphertextIdeally only authorized parties can decipher a ciphertext back to plaintext and access the original information.
Cybersecurity Key Ponents And Relationships Download Scientific Diagram Find the most up-to-date statistics and facts on the impact of cyber crime on consumers in the United States.
| Topic: 2The Computer Security InstituteFBI Computer Crime Security Survey found the average theft of a laptop to cost a company 31975. Cybersecurity Key Ponents And Relationships Download Scientific Diagram Computer Crime And Security Survey 2008 |
| Content: Synopsis |
| File Format: PDF |
| File size: 2.2mb |
| Number of Pages: 7+ pages |
| Publication Date: June 2021 |
| Open Cybersecurity Key Ponents And Relationships Download Scientific Diagram |
 |
19CSI Computer Crime and Security Survey 2008.


Key Risk Indicators For Confidentiality Information And Cyber Security Risk Download Table 4704 a global leader in Internet content security reported on July 7 that cybercriminals are not only leveraging new technologies to propagate cybercrime but are also reinventing forms of social engineering to cleverly.
| Topic: Computer security refers to the protection of data networks computer programs computer power and other elements of computerized information systems. Key Risk Indicators For Confidentiality Information And Cyber Security Risk Download Table Computer Crime And Security Survey 2008 |
| Content: Answer Sheet |
| File Format: DOC |
| File size: 1.7mb |
| Number of Pages: 21+ pages |
| Publication Date: April 2019 |
| Open Key Risk Indicators For Confidentiality Information And Cyber Security Risk Download Table |
 |

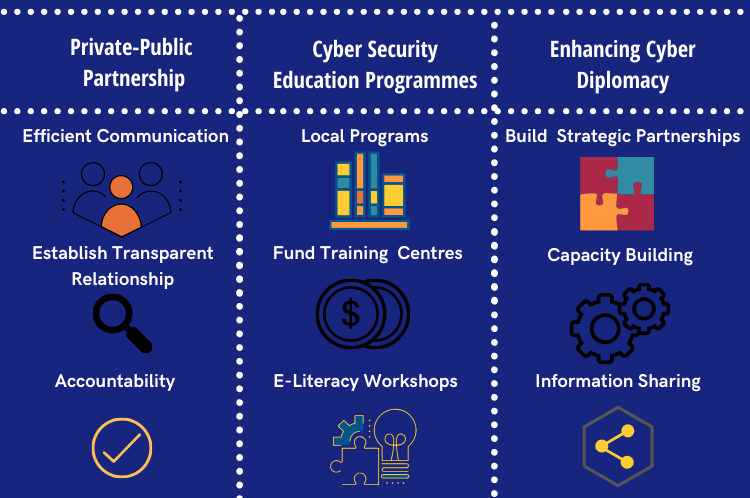
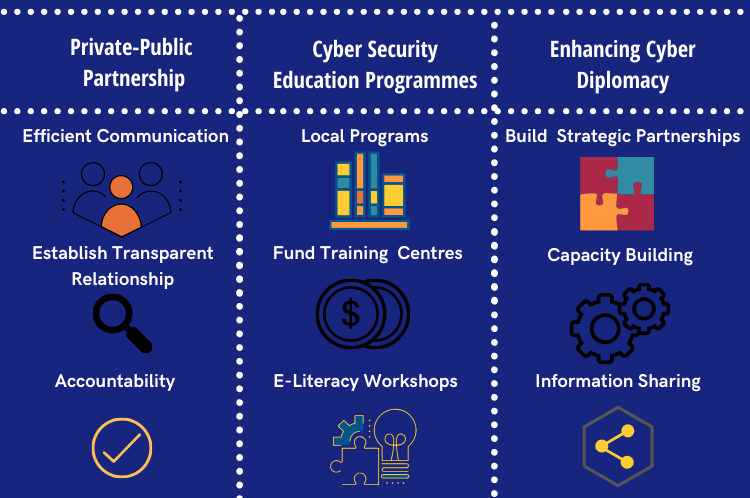
Mitigating The Risk Of Cyber Crime In Sri Lanka The Lakshman Kadirgamar Institute Laptop or mobile hardware theft D.
| Topic: Encryption does not itself prevent interference but denies the intelligible. Mitigating The Risk Of Cyber Crime In Sri Lanka The Lakshman Kadirgamar Institute Computer Crime And Security Survey 2008 |
| Content: Solution |
| File Format: PDF |
| File size: 810kb |
| Number of Pages: 23+ pages |
| Publication Date: March 2020 |
| Open Mitigating The Risk Of Cyber Crime In Sri Lanka The Lakshman Kadirgamar Institute |
 |

Proposed Cyber Security Agency Anization Chart For Turkey Download Scientific Diagram Crimes in cyber space.
| Topic: 1The financial threat loss to organizations could be significant. Proposed Cyber Security Agency Anization Chart For Turkey Download Scientific Diagram Computer Crime And Security Survey 2008 |
| Content: Solution |
| File Format: Google Sheet |
| File size: 2.3mb |
| Number of Pages: 25+ pages |
| Publication Date: April 2017 |
| Open Proposed Cyber Security Agency Anization Chart For Turkey Download Scientific Diagram |
 |

Handbook Of Puter Works And Cyber Security Principles And Paradigms Brij Gupta Springer In a study surveying 329 private and public organizations published by Intel in 2010 71 of employee laptops were lost or stolen before the end of their usefulness lifespan.
| Topic: The law enforcement world is scrambling to catch up. Handbook Of Puter Works And Cyber Security Principles And Paradigms Brij Gupta Springer Computer Crime And Security Survey 2008 |
| Content: Synopsis |
| File Format: DOC |
| File size: 2.6mb |
| Number of Pages: 45+ pages |
| Publication Date: January 2020 |
| Open Handbook Of Puter Works And Cyber Security Principles And Paradigms Brij Gupta Springer |
 |

The Critical Security Controls At The Gartner Security Conference Sans Institute Security Conference Cyber Security Security Viruses unauthorized access laptop or mobile hardware theft and theft of proprietary information 2.
| Topic: List the major findings of the CSI 2010 survey. The Critical Security Controls At The Gartner Security Conference Sans Institute Security Conference Cyber Security Security Computer Crime And Security Survey 2008 |
| Content: Answer Sheet |
| File Format: PDF |
| File size: 2.6mb |
| Number of Pages: 10+ pages |
| Publication Date: April 2019 |
| Open The Critical Security Controls At The Gartner Security Conference Sans Institute Security Conference Cyber Security Security |
 |

The Five Mandates And The Six Elements Of The Cyber Security Incident Download Scientific Diagram
| Topic: The Five Mandates And The Six Elements Of The Cyber Security Incident Download Scientific Diagram Computer Crime And Security Survey 2008 |
| Content: Answer |
| File Format: PDF |
| File size: 2.8mb |
| Number of Pages: 27+ pages |
| Publication Date: May 2018 |
| Open The Five Mandates And The Six Elements Of The Cyber Security Incident Download Scientific Diagram |
 |

Cyber Security Indicators Saint Eu Project
| Topic: Cyber Security Indicators Saint Eu Project Computer Crime And Security Survey 2008 |
| Content: Learning Guide |
| File Format: DOC |
| File size: 3.4mb |
| Number of Pages: 8+ pages |
| Publication Date: May 2017 |
| Open Cyber Security Indicators Saint Eu Project |
 |

Top 10 Cyber Security Threats Amid Covid 19 Pandemic Download Scientific Diagram
| Topic: Top 10 Cyber Security Threats Amid Covid 19 Pandemic Download Scientific Diagram Computer Crime And Security Survey 2008 |
| Content: Summary |
| File Format: Google Sheet |
| File size: 3.4mb |
| Number of Pages: 13+ pages |
| Publication Date: August 2019 |
| Open Top 10 Cyber Security Threats Amid Covid 19 Pandemic Download Scientific Diagram |
 |

Relationship Between Cyber Security And Other Security Domains 38 Download Scientific Diagram
| Topic: Relationship Between Cyber Security And Other Security Domains 38 Download Scientific Diagram Computer Crime And Security Survey 2008 |
| Content: Explanation |
| File Format: PDF |
| File size: 800kb |
| Number of Pages: 20+ pages |
| Publication Date: August 2017 |
| Open Relationship Between Cyber Security And Other Security Domains 38 Download Scientific Diagram |
 |

It Security Infographic Cyber Security Puter Security Web Security
| Topic: It Security Infographic Cyber Security Puter Security Web Security Computer Crime And Security Survey 2008 |
| Content: Learning Guide |
| File Format: DOC |
| File size: 1.4mb |
| Number of Pages: 29+ pages |
| Publication Date: July 2021 |
| Open It Security Infographic Cyber Security Puter Security Web Security |
 |
Cpv Codes For The Cyber Security Sample Download Scientific Diagram
| Topic: Cpv Codes For The Cyber Security Sample Download Scientific Diagram Computer Crime And Security Survey 2008 |
| Content: Learning Guide |
| File Format: Google Sheet |
| File size: 810kb |
| Number of Pages: 27+ pages |
| Publication Date: March 2017 |
| Open Cpv Codes For The Cyber Security Sample Download Scientific Diagram |
 |
Its really simple to get ready for computer crime and security survey 2008 Key risk indicators for confidentiality information and cyber security risk download table it security infographic cyber security puter security web security infographic are you cybersafe cyber security awareness puter security cyber security the critical security controls at the gartner security conference sans institute security conference cyber security security cpv codes for the cyber security sample download scientific diagram japan number of cybercrime consultations 2018 statista proposed cyber security agency anization chart for turkey download scientific diagram mitigating the risk of cyber crime in sri lanka the lakshman kadirgamar institute

Post a Comment
Post a Comment